Eliminate Blind Spots with a full Attack Path Management (APM) Plan
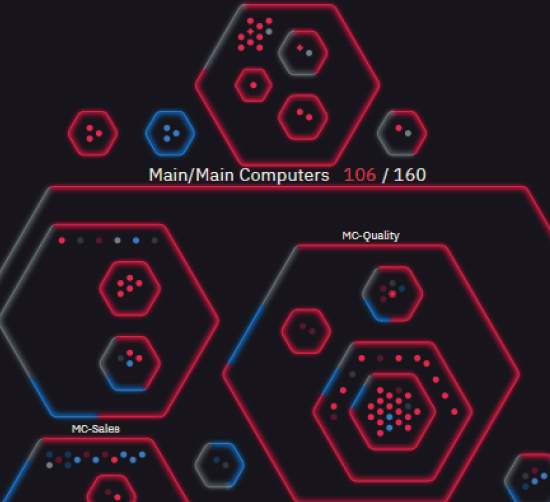
Attack path management (APM), or attack path mapping, is a vital process organizations should use to get insight into their security weaknesses as seen through the eyes of an attacker. When business owners are able to fully understand what potential bad actors see, they can build a stronger defense plan. As a result, attacks can be shut down quicker before severe damage occurs.
An “attack surface” just describes the number of possible attack points and vectors an unauthorized user can access within any of your systems and, in turn, breach data. As such, it’s our job to reduce the attack surface, so it’s easier to protect. All businesses, small or large, should have mechanisms in place to constantly monitor an attack surface, ensuring threats are identified and blocked as soon as possible. An attack surface is split into two primary categories: digital and physical.
Attack Path Mapping vs. Penetration Testing
Snapshot in time penetration testing just doesn’t work. The tests are time constrained, tester constrained, and opportunity constrained. The results are limited to what the specific testers find during a specific window. The deliverables aren’t that great, either.
Traditionally, the penetration testers will provide you with a laundry list of things to remediate, often in no particular order, and then they go away until the next year’s test rolls around.
Here at Cyber Guards, we test our client environments in a consistent, persistent, do no harm manner every single day. We then stick around to help you remediate the findings and validate your remediation efforts. Continuous attack path management is the fastest route to long term improvement of your digital environment.
The Steps of APM
Your first step is to create complete visibility into your entire hardware ecosystem, and then perpetually monitor the network. Knowing APM focuses on the perspective of the attacker, not the defender, penetration testing and red teaming – when you take a holistic adversarial look at your entire IT landscape – provide insight into an attacker’s potential mindset. Once you’ve mapped your attack surface, it is critical to test for vulnerabilities and then continuously monitor performance. Threat surface management is key to identifying current and future risks, including:
- Identify high-risk areas to test for vulnerabilities.
- Identify changes and any new vectors that may have been recently created.
- Determine which roles and types of users from your team can access your systems.
- Mitigate against all future cyberattacks.
It’s never too late to identify the entirety of your attack surface. Understanding and inventorying your equipment and software is a great first step in the process.
Attack Path Management Key Features
Why You Need an Attack Path Management Plan
While you get busy remediating findings from a penetration test, the report begins to age. The results are less valuable, and new issues may have been introduced to your environment that you are not seeing yet. With a complete attack path mapping plan, you will have the most up-to-date information on what is going on in your environment at any given time.